Continuing my set of instructions for installing Lync Mobility. Here we cover setting up our servers. See the previous post for how to update your servers and Part 1 for details about configuring DNS
Overview of changes
- Add two new DNS records – one internal, one external
- Either A records or C-Names
- Patch everything to Lync RTM CU4
- Define the “Internal ports” used for mobile clients
- Install mobility bits on Front-Ends & Directors
- Enable Dynamic compression in IIS
- Re-request certificates to support new mobile DNS names
- Configure your reverse proxy
- Configure push notifications
- Test! (Kinda)
Sorting out Certificates
Note: If you are using internal certificates for your Lync servers & your wifi network (that mobile’s will connect to) is internal then you either need to make sure the mobile clients trust your internal PKI, or change to use “public” certificates.
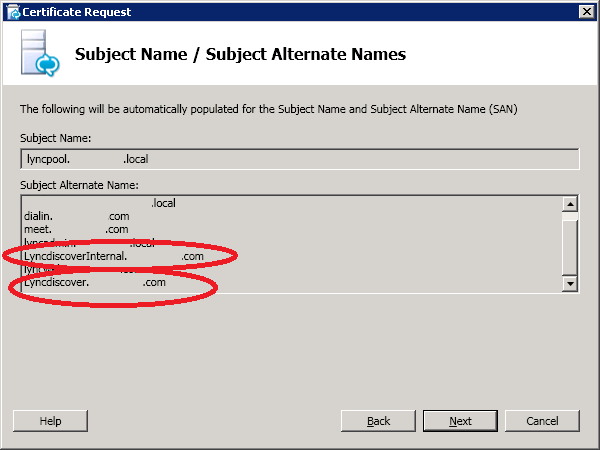
Now we need to add the new SAN’s (Subject Alternative Name) – Lyncdiscoverinternal & Lyncdiscover to our Lync server certificate. There are lots of ways to do this but the simplest is probably to use the Lync certificate wizard
From the start menu run the “Lync Deployment Wizard”
Then under “Install or Update Lync Server System” re run “Step 3”
Walk through the wizard using the same parameters as when you first deployed Lync. On the last step check that the new names are part of the request
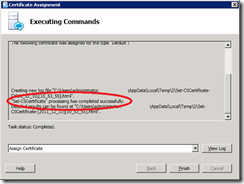
Complete the request & then run the “Assign certificate” wizard & make sure it’s completed successfully
To tidy things up you might want to go into the local certificate store and delete out the old certificate just so you don’t get confused in future
You can also go and check in IIS that the new certificate is being used against the internal & external site bindings
For good measure stop & restart the Lync services
(Stop-CsWindowsService & Start-CsWindowsService)
Configure the reverse proxy
In my topology my reverse proxy is an ISA server configured with a wildcard certificate for *.domain.com. I have a single listener for all Lync reverse proxy stuff so I should just need to add the new domain into the list of accepted names for the rule.
The official Lync mobility documentation makes no mention about whether wildcard certificates are supported or not includes a reference to *.domain.com being a suitable alternative so looks like wildcards are allowed.
Microsoft at least made allowanced for people who had already purchased expensive UC certificates by allowing the initial connection to the new DNS name over HTTP so the client can be redirected to another name that is covered by an SSL certificate.
Open the rule up and add-in the new “LyncDiscover” domain name
Apply the configuration changes
Continue to Part 4…












Excelent work. If a proxy server dosent exist what is the process
Hello,
That depends how you are publishing the other Lync external services? If you already have external access you just need to add “MCX” and “AutoDiscover” to the allowed URLS on that device.
Ben
Yes, You can do the Lync Mobility without a Reverse Proxy. In that scenario 80 & 443 ports should be forward to 8080 & 4443 ports in Lync FE server. But this is not recommended method to deploy. Anyway it will work.
Ok, but adding SANS requires that you regenerate and replace the internal cert, right ?
Also, I guess Im a little confused on what cert names need to be assigned internally, on the front end, versus the outside.
by outside, I mean the reverse proxy.
Hi,
Adding SANs to your internal front end servers will require generating a new cert but this isn’t normally an issue as they are private certs. Also I dont normally bother with lyncdiscoverinternal.domain.tld as I force mobile clients on the internal network to talk to the reverse proxy (which has a pulbic cert on) to avoid any trust issues.
As for your reverse proxy, it normally has a cert that covers the simple URL’s like: meet.domain.tld, dialin.domain.tld, lyncRP.domain.tld, lyncdiscover.domain.tld etc… This link from MS for the reference edge architectures is very good: http://technet.microsoft.com/en-us/library/gg398519
Ben
Thanks for the response Ben. We use Verisign public certs for everything and so far on this Lync deployment I’m up to over 25 !! On the reverse proxy I’ve got 21 alone (mostly for the the lyncdiscover. entries for each sip domain). I admit I’m very confused about the certs but it’s not to late to revoke them. The wildcard cert seems like a good alternative if it’s supported.
If your set for federation drop me an email via the address on the “about page” I’ll give you my SIP address. Happy to chat about it if you like
Ben
Please I need your assistance urgently with federation.
We do not have firewall and I need to know how else I can achieve Mobility and federation without ISA
You could use IIS with the ARR module installed, this is more than capable of doing the Lync RP role. There are a lot of good tutorials that walk you through the process.
If you don’t have a firewall how have you setup your Lync Edge server?